31 AUGUST 2018, BENNETT GARNER
A Sybil attack is an attempt to control a peer network by creating multiple fake identities. To outside observers, these fake identities appear to be unique users. However, behind the scenes, a single entity controls many identities at once. As a result, that entity can influence the network through additional voting power in a democratic network, or echo chamber messaging in a social network.
The United States’ recent trouble with Russian election influence via fake accounts on social media is an easy-to-understand example of a pseudo-Sybil attack. Although the fake accounts and bots didn’t hack into Facebook or Twitter, they still used multiple identities to influence the entire network. Because Sybil attacks are so subversive and easy to conceal, it can be difficult to tell when a single entity controls many accounts. Indeed, Facebook didn’t even realize the extent of fake accounts on their platform until internal investigations months after much of the damage was already done.

Fake news.
The name “Sybil attack” comes from a book, Sybil, about a woman with dissociative identity disorder. Microsoft researchers first investigated and wrote about the implications of Sybil attacks on peer networks in the early 2000s. In this brief guide, we’ll look at the implications of Sybil attacks and how networks can prevent such attacks. If you’re considering using a blockchain platform, it’s important to understand their approach to Sybil threats and undue influence through identity creation on the network.
Disproportionate Control
A Sybil attack grants undue influence to a single entity simply because that entity controls many pseudonyms. We hear all the time about fake Reddit accounts that upvote posts on behalf of a given company or cause. Amazon sellers can buy fake reviews from accounts around the world. These pseudonyms are hard to detect and remove.
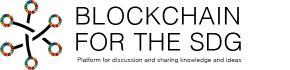
While election meddling on Facebook and fake reviews on Amazon are bad enough, a successful Sybil attack against a blockchain or file transfer network would allow bad actors disproportionate control over the network. If these fake identities receive recognition from the network, they might be able to vote on behalf of various proposals or interrupt the flow of information across the network.
Sybil nodes try to influence informaiton flow across a network
Sybil nodes might also surround and try to influence the information reaching other nodes on the network, gradually influencing the ledger or database through censorship.
Prevention
Blockchains and peer networks have various options when it comes to preventing Sybil attacks. Each option comes with its own benefits and drawbacks. Hybrid approaches to Sybil prevention, incorporating each of three key elements, are common to address concerns.
1. Cost to Create an Identity
The first way to mitigate a Sybil attack is to raise the cost of creating a new identity. Since identities can map to entities on a many to one ratio, we need a way to make it resource intensive to create too many identities. The challenge here, though, is there are many legitimate reasons why you might want to operate multiple identities. Redundancy, resource sharing, reliability, and anonymity are all good reasons to create multiple identities on a peer network.
Blockchains use the cost of creation as a Sybil protection feature through mining. In proof of work algorithms, in order to create a new identity on the mining network, you’ll need another computer with processing power to contribute. This attaches a significant cost to adding hundreds or thousands of pseudonymous nodes that might be able to influence the adoption of a fork or other blockchain vote.
The same goes for proof of stake, where purchasing computing power is replaced by staking currency. There’s a cost to join the network and have a vote. That resource requirement limits the number of accounts a bad actor can create.
2. Chain of Trust
A second way to fight Sybil attacks is requiring some type of trust before allowing a new identity to join the network. This usually takes the form of a reputation system, where only established, long-term users can invite or vouch for new entrants to the network. Other variations rely on a probationary system where new accounts are possible, but they must remain active and unique for a certain period before they receive voting privileges.
Two-factor authentication is one tactic for Sybil prevention
Chain of trust also extends to outright identity verification. Some peer networks require you to submit identification before joining. Others allow you to join if you can answer a two-factor authenticated security code. Still others restrict account creation based on IP address.
All of these require some level of identity verification or trust building before an account receives voting privileges, making the creation of pseudonyms more challenging.
3. Unequal Reputation
The final way to mitigate the threat of Sybil attacks is by weighting user power based on reputation. Users that have been around the longest and proven themselves receive more voting power on communal decisions. This makes the system a meritocracy instead of a pure democracy, and it lowers the power of new users. As a result, many new or less-active accounts don’t grant a Sybil attacker any advantage against reputable older, more active accounts.
Sybil Attacks Are Hard to Prevent
Sybil attacks involve false identities and hidden motives. As such, they can be difficult to detect and prevent until they’re already ongoing and apparent. Still, networks that implement a combination of these prevention measures see increased protection from Sybil attacks, mitigating the potential severity of the attack if and when it comes.
Credits: Coincentral.com
Discuss: Threats of Sybil attacks